Not due to shortages in IPv4 address, because that’s relative (looking at the 4 million IPv4 addresses Amazon bought this year from AR|DC‘s AMPRNet), but more due to personal interest and being able to equip all your devices with public IP’s (and not having to use NAT masquerading) is interesting. During my PTO, I had some spare time, so it’s time to implement IPv6 at home and in the lab.
I always had a great interest in networking. It started at school already, learning about Ethernet, Tokenring and so on. From my first internship at a university which already had an excellent internet IP connectivity back in the days to implementing NetWare based IPX based networks at my first employer.
Recently I realized that there was much to learn about IPv6 after looking into it a bit more. Essentially it does the same compared to IPv4, but it is implemented very different. After learning that my ISP supports tunneled IPv6 connectivity (more to that in part 2) it was time to start learning.
The series
In this IPv6 series I’d like to tell you about my “journey” to implement the protocol. I already had some knowledge of it, but not extensively. As a first step I implemented it at my home. The plan is to work my way back to my lab in the data-center.
My implementation steps will be split into several parts of which this one is the first. The other parts will soon follow.
- Part 1: IPv6 Primer (this post)
- Part 2: IPv6 at home using 6RD
- Part 3: Native IPv6 in the Lab
- Part 4: IPSec VPN
- Part 5: IPv6 with NSX-T
Probable outline of next parts (subject to change)
- Part 6: IPv6 with Cloud Director
To be able to assign and use IPv6 in my lab, it’s an advantage my employer (Equinix) is an ISP. This way I’m able to connect my lab to the internet and register a global unicast (public) /48 IPv6 block in the RIPE database. This leaves 16 bits for the subnet, since /64 subnets are assigned to hosts. The IPv6 address space itself is maintained by IANA and can be found it the “Internet Protocol Version 6 Address Space“.
The way IPv6 blocks are assigned, can be seen below. The sites are in fact the organizations who use the IP block.
RIPE is the Regional Internet Registries (RIR) for The Netherlands, which is responsible for assigning IP blocks to their members or Local Internet Registry (LIR’s). In the world the are 5 RIR’s, which all have their own region to serve.

Background
In this series I assume you have common knowledge of switching (L2), routing (L3) and IP networks. Which includes sub-netting, CIDR notations and numeral systems like binary / hexadecimal.
IPv6 Notation
In the above picture you can see an example of an global unique address has a length of 128 bits and is divided into:
- The first 48 bits are the network prefix
- The 16 bits after that is the subnet prefix
- The last 64 bits are the host prefix
IPv6 basic differences
Besides having a 128-bit address schema compared to the 32-bit for IPv4, there are a lot of differences. Let’s see the main ones.
| Property | IPv4 | IPv6 |
| #Addresses | 232 | 2128 |
| IP Discovery protocol | ARP | NDP |
| IP Discovery method | Broadcast | Multicast |
| IP Multicast protocol | IGMP | MLD |
| DNS record | A record | AAAA record |
| Stateful Host config method | DHCP | DHCPv6 DHCPv6-PD |
| Stateless Host config method | – | SLAAC |
| Generic subnet size | /24 | /64 |
| First address in IP subnet | Network address | Router AnyCast address |
| Last address in IP subnet | Broadcast address | Local subnet multicast address: ff02::1 |
| Use of NAT | Often needed for RFC 1918 private IP | Rarely needed |
| Firewall impact | Internal IP’s “protected” by SNAT masquerading | Internal IP’s need to be firewalled |
| Packet fragmentation | Supported (DF bit in IP header) | Not supported |
IPv6 Address Types
The are a couple of important address differences because of their intended use. It can be compared to the the RFC1918 private addresses. In the IPv6 world there are some important prefixes to remember, of which IANA maintains the current list of special purpose IPv6 address. The most common are:
| Prefix | Global routeable | Purpose |
| 2000::/3 | Yes | Global Unicast Addresses (IANA current IPv6 allocation) |
| 2001:db8::/32 | No | Documentation |
| fc00::/7 | No | Unique Local Addresses (Private IPs) |
| fe80::/10 | No | Link-Local Addresses |
| ff00::/8 | Yes | Multicast Addresses |
ICMPv6
Just like in an IPv4 world, ICMPv6 is an important part of the IP protocol suite. ICMPv6 is responsible for error reporting and diagnostics and works closely together with NDP.
Some of it’s most used examples features are:
- Echo Request / Reply (ping)
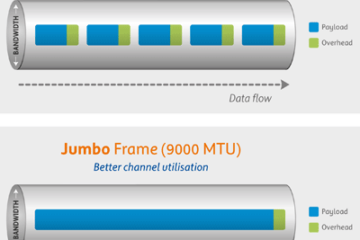
- Path MTU Discovery
- Notification to sender when packet dropped due to
- Destination unreachable
- MTU size (Packet too Big)
- Hop count exceeded
- IP Discovery using NDP
- Duplicated address detection (DAD)
- Multicast using MLD
IP Discovery
In an IPv4 environment, ARP is used within the L2 broadcast domain to discover the MAC address for a given IP address. ARP works by sending a broadcast frame to MAC address FF:FF:FF:FF:FF:FF to ask who has IP address 1.2.3.4 and expects to get the correct MAC if the IP is available.
NDP
In an IPv6 environment there is no ARP and no broadcast at all. In this case the NDP protocol is used which in fact is an extension of ICMPv6. Together with the Link-local address (fe80::/64) it uses multicast to discover the MAC for an IPv6 address. NDP uses the IPv6 link-local address which is unique within the L2 domain, which is a reason why it is required for every hosts that has an IPv6 stack.
In short, NDP is an extension of ICMPv6 and responsible for gathering various information required for internet communication. Including the configuration of local connections and the domain name servers and gateways used to communicate with more distant systems (Source: Wikipedia).
Multicast
In an IPv4 world IGMP is used to implement multicast in the network. In an IPv6 enabled network MLD (Multicast Listener Discovery) is used instead. MLD is just like NDP an extension of the ICMPv6 protocol.
When IPv6 is implemented, take into account the multicast configuration on your switches. That’s important since many of the IPv6 functions depend on it. As mentioned in the previous section, IPv6 does not use broadcast anymore, but use MLDv1 or MLDv2 instead. Both are derived from IGMP v2 and v3 respectively.
If possible use MLD capable switch and configure MLD snooping accordingly. This prevents flooding of multicast packets to all ports in the VLAN instead of only the port on which members of the multicast group reside.
Dynamic IP configuration
In IPv4 networks, DHCP is basically the only used method for dynamic host configuration. In IPv6 there are 2, which are DHCPv6 (stateful) and SLAAC (stateless) and both can co-exist. In both cases the duplicate address detection (DAD) is used to determine if an IPv6 address is already used by another host. DAD is used for all types of IPv6 addresses (link-local, unicast and so on).
Stateful
DHCPv6 is considered as a stateful because some DHCP server process must run on a host or device that keeps track of assigned IP addresses. The server assigns IP’s address and additional parameters to hosts, like: DNS server / suffix and NTP, which is basically the same compared to IPv4.
An extension to DHCPv6 is Prefix Delegation, DHCPv6-PD in short. In this case the DHCP server also can assign complete prefixes to network devices, instead of only assigned addresses to hosts. A good use-case could be an ISP that assigns a complete prefixes (/64) to it’s customer routers (CPE’s).
Stateless
One of the main advantages of IPv6 is stateless IP configuration using SLAAC (Stateless Autoconfiguration). In other words, no process is running on the router that assigns addresses, compared to DHCP (stateful). Using SLAAC, the hosts will select and configure IP addresses themselves.
It works in such a way that the hosts and router must be in the same L2 domain, just like with DHCP and IPv4. The router interface is assigned a /64 prefix by the network ad ministrator. Using the hosts link-local address (fe80:: ) together with NDP, ICMPv6 and multicast, the host determines what the prefix is and who the router is.
Using the EUI-64 method, the host selects an IP address itself and checks if the address is unique within the L2 domain using multicast and it’s link-local address. From the router it learns also parameters like MTU size and name server.
More info
To get more information about the protocol, you could check out the “IPv6 Introduction” course on PluralSight, check out the vendor independent book “IPv6 Essentials” by Silvia Hagen or visit Valter his blog on various IPv6 related topic howdoesinternetwork.com/ipv6
To conclude
Hopefully you have a bit more of the understanding of the IPv6 basics. The more I read about it, the more it makes sense to adopt it. For example getting rid of broadcast and IP fragmentation seems like a good thing and new features like the large address space, SLAAC and DHCPv6-PD are great improvements.
Also make sure you implement and configure your firewall correctly. Using public IPv6 addresses within your network could make your hosts “visible” due to the lack of NAT Masquerading. Especially in larger networks make sure to implement MLD snooping on your switches to prevent flooding.
The downside of IPv6 is it’s incompatibility with IPv4 and added complexity. At least to me, due to the complexity in the address format, sub-netting and the required use of multicast was a reason not digging into it sooner.
Useful links
Good explanations about the various IPv6 protocols by Valter Popeskic
NDP – Neighbor Discovery Protocol
IPv6 – SLAAC Stateless Address Autoconfiguration
IPv6 – SLAAC EUI-64 Address Format
The New Way of Generating IPv6 – SLAAC EUI-64 Address Format
IANA
Internet Protocol Version 6 Address Space
Cisco documentation
DHCPv6 Based IPv6 Access Services
IPv6 Access Services: DHCPv6 Prefix Delegation
DHCPv6 using the Prefix Delegation Feature Configuration Example





0 Comments