When you’ve lost the root password of your NSX-T 3.x Manager, Edge or Cloud appliance (including 2.5.2+) things have gotten a lot easier. Nowadays a password reset method is now build into the Edge, Manager and Cloud Manager appliance. In the versions before 2.5.2, it was a pretty tedious procedure involving a lot of steps, including and booting the appliance with a Ubuntu server ISO.
In my case the passwords of all local users on the Edge nodes in my lab were expired (90 days by default). Secondly the expected passwords were incorrect, so I could not change the passwords of the admin and root accounts. The expired Edge nodes passwords generated alarms in NSX-T Manager, which prevents upgrading the NSX-T Manager appliance to a higher version.
The last section describes how to prevent password expiration for an appliance from even happening. This can be configured via the appliance CLI.
The current procedure
When the appliance admin or audit account are expired or locked, you can reset these accounts by logging in with the root account and perform a simple reset or even prevent those accounts from expiring (see the section below).
If you cannot login with root anymore, the new root password reset procedure is a lot easier, more safe and faster. The reset procedure is documented in the NSX-T Administration guide. All former procedures that mention to mount the appliance root filesystem (with an Ubuntu Server ISO) work fine, but are obsolete.
The steps to reset the appliance root password are:
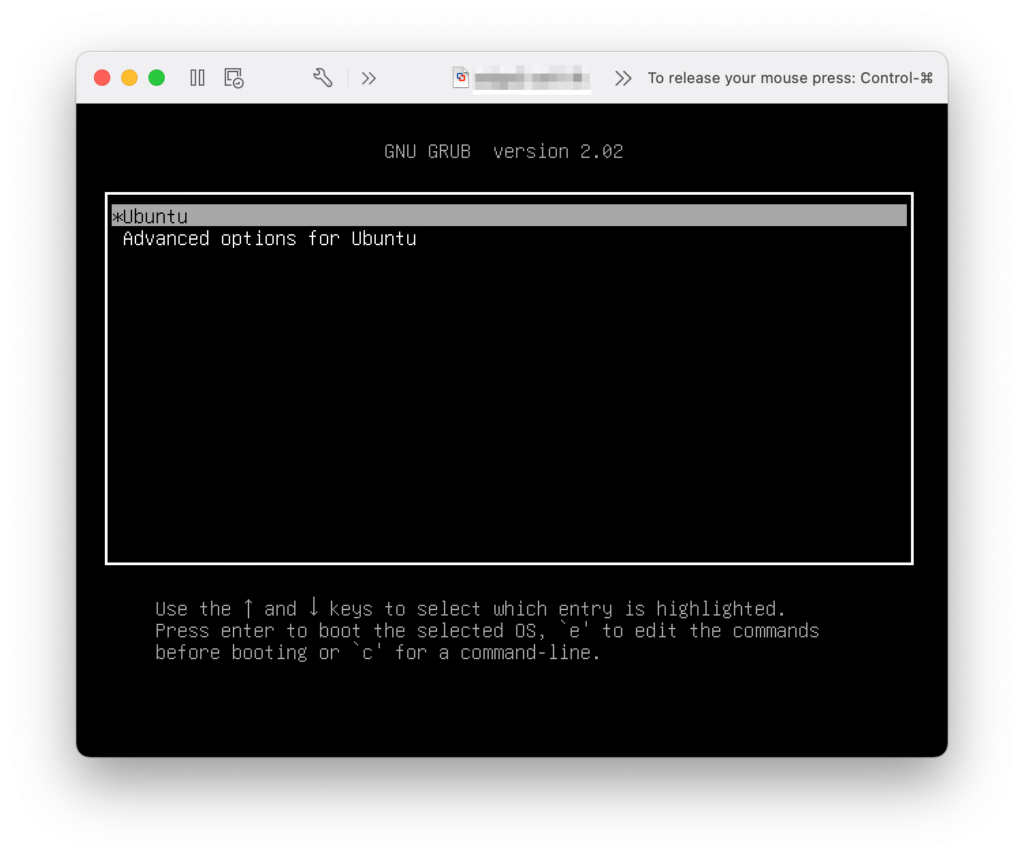
- Open a console to the appliance (I used Fusion to connect to my vCenter)
- A dedicated console window was needed (before key input in the following steps worked). See figure 1
- Boot / reboot the NSX appliance
- Press en hold “Esc” or “Shift” during the POST
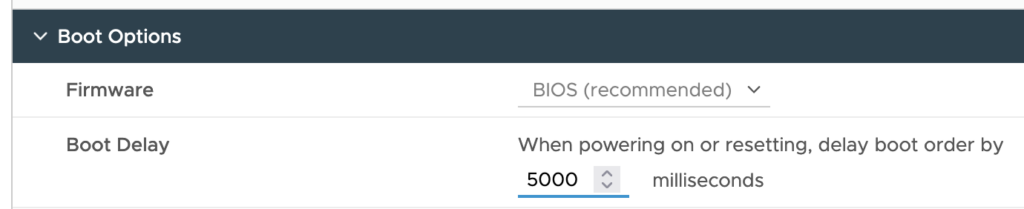
- Changing the VM boot delay for the NSX appliance in vCenter gives you a bit more time. See figure 2
- The GRUB boot menu is shown and press a key within 30 sec. to prevent auto booting the NSX appliance
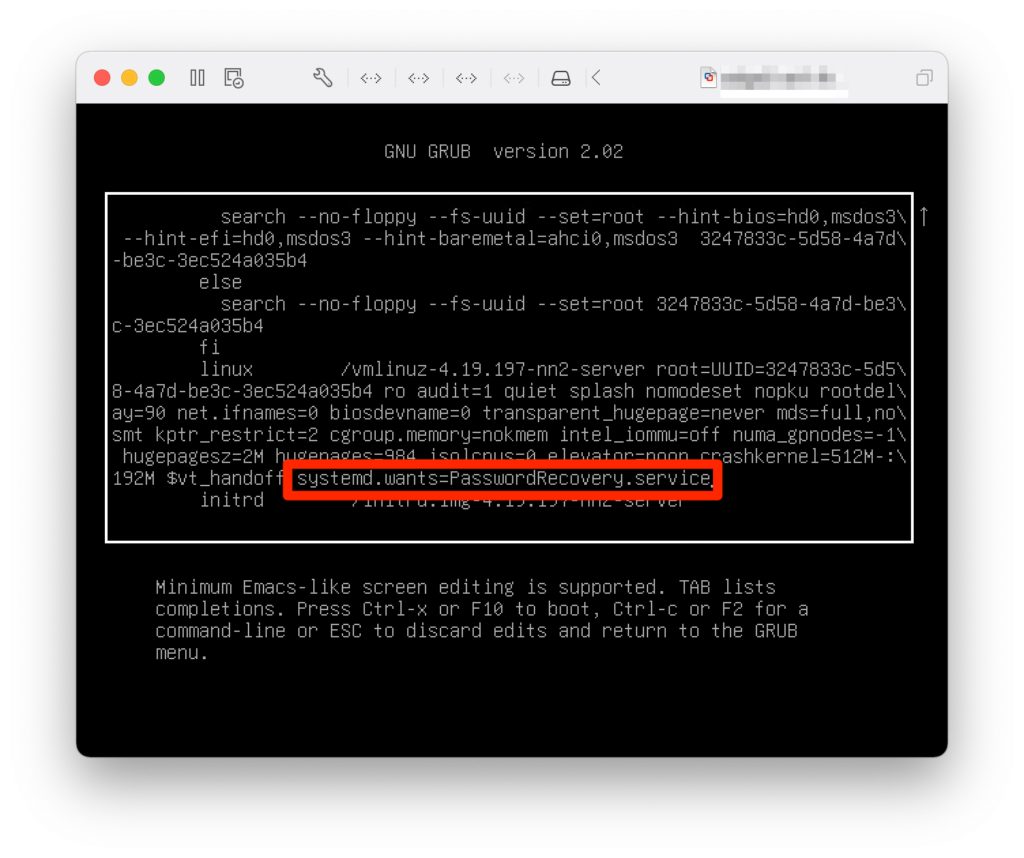
- Press “e” to edit the GRUB boot loader config
- Enter “root” as GRUB user and “VMware1” as password for NSX up to version 3.1. As of NSX 3.2 the password is “NSX@VM!WaR10“
- Search for the line that starts with “linux /vmlinuz…” and add the following to the end of that line “systemd.wants=PasswordRecovery.service”
- See figure 3
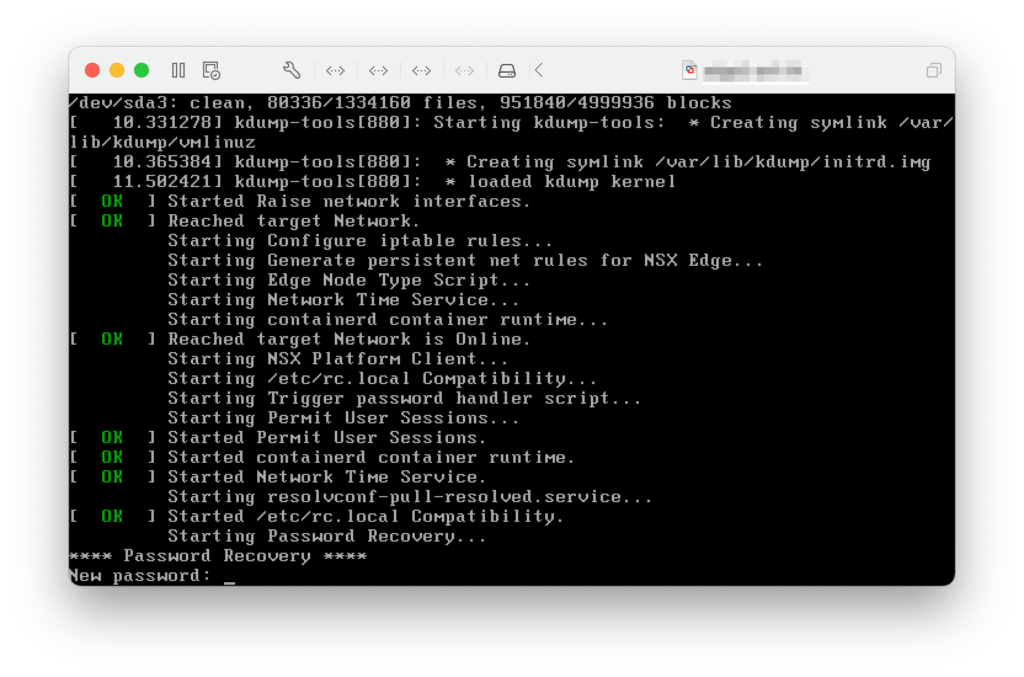
- Press “Ctrl – X” to boot the appliance
- Change the appliance root password
- See figure 4
- Login with the root account and change the password of the local admin and audit accounts
Prevent password expiration
Now the password recovery is done and full access to the appliance is re-gained, let’s prevent the expiration from happening again. On the appliance, access the console either locally or via SSH (if enabled) and login in as “admin”. The example below shows disabling password expiration for the Manager appliance.
<workstation>:~ <user>$ ssh admin@nsx-appliance admin@nsx-appliance's password: NSX CLI (Manager, Policy, Controller 3.1.3.5.0.19068437). Press ? for command list or enter: help nsx-appliance> clear user admin password-expiration nsx-appliance> clear user root password-expiration nsx-appliance> clear user audit password-expiration nsx-appliance>
Useful links
NSX Admininistration guide: Resetting the Passwords of an Appliance
NSX Administration guide: Manage Local User’s Password or Name


4 Comments
Henrik Rundqvist · April 16, 2023 at 4:28 pm
Thanks for your guide. Just a brief update; The default GRUB password is now ‘NSX@VM!WaR10’ and is documented in https://docs.vmware.com/en/VMware-NSX-T-Data-Center/3.2/administration/GUID-8816B842-2EC4-40A8-A618-F68DB29FABD2.html
Daniël Zuthof · April 16, 2023 at 4:48 pm
Hi Henrik,
Thanks for the feedback. The blog post is updated.
Cheers, Daniël
Joshua Szanto · May 9, 2023 at 5:30 pm
So, what if the GRUB password has been changed and none of the defaults work?
Daniël Zuthof · May 9, 2023 at 9:50 pm
Hi Joshua,
I haven’t tested, but I guess booting into single user mode using a Ubuntu ISO could be the way forward. It’s explained in page 544 of the NSX-T 2.4 Admin Guide.
As always, if it’s a production system, have the NSX config backup at hand, contact VMware support and / or test on a clone VM to prevent data loss.
Cheers, Daniel